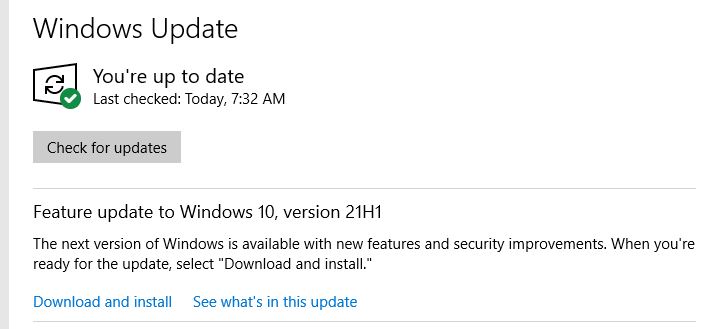
The lead-in graphic for this story shows some big news. That is, the Feature update to Windows 10, Version 21H1 is now available. This applies to Windows Insiders in the Beta Insider Preview channel, I hasten to add. And indeed, the foregoing item showed up on my Beta Channel test machine this morning. Hence the proclamation that 21H1 hits Beta Preview channel.
When 21H1 Hits Beta Preview Channel, Then What?
There are two kinds of implications for this occurrence. One is technical, and the other is a matter of historical analysis and implication. On the technical front, this means that the upcoming 21H1 is more or less locked down. That is, what we see in this preview release is also pretty much everything we’ll see in any upcoming public release. On the historical front, public releases typically have followed previews somewhere from 4 to 6 weeks after the preview appears. That puts initial public release of 21H1 somewhere between March 18 and April 1, by my reckoning.
Upon reflection, I kind of like an April 1 date (April Fool’s Day).
The Beta Channel Upgrade Experience
The screencap you see at the head of this story is the one that appeared on my Beta Channel test PC. For up-to-date Beta Channel PCs, this update is undoubtedly an enablement package that simply turns on features already present in the Insider Preview OS.
Why say “enablement package?” I say that because it completed the pre-reboot portion of the install in under two minutes on a Surface Pro 3 (vintage 2014) machine. The “Working on Updates” portion was pretty speedy, too (less than a minute). And the post-reboot drill took about 30 seconds (just a hair slower than a normal rebooot, in other words). You won’t have to spend much time twiddling your thumbs while waiting for this “feature upgrade” to install!
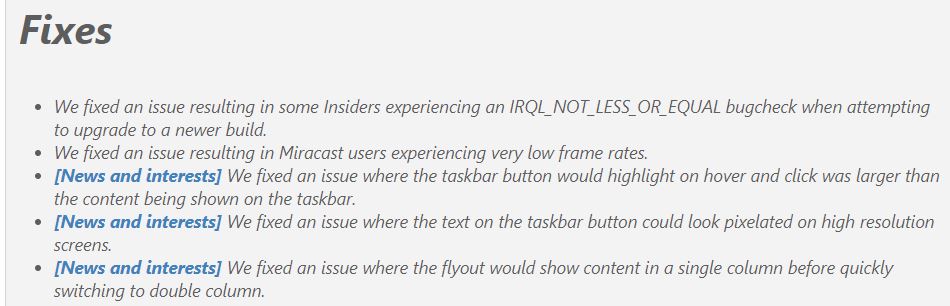
I’m jazzed to understand that 21H1 is in the offing, and should be making its way into public release somewhat sooner than I’d expected. My congrats and thanks to the #WindowsInsiders team in general. Take a read of Brandon Leblanc’s Announcement post for more Insider info.