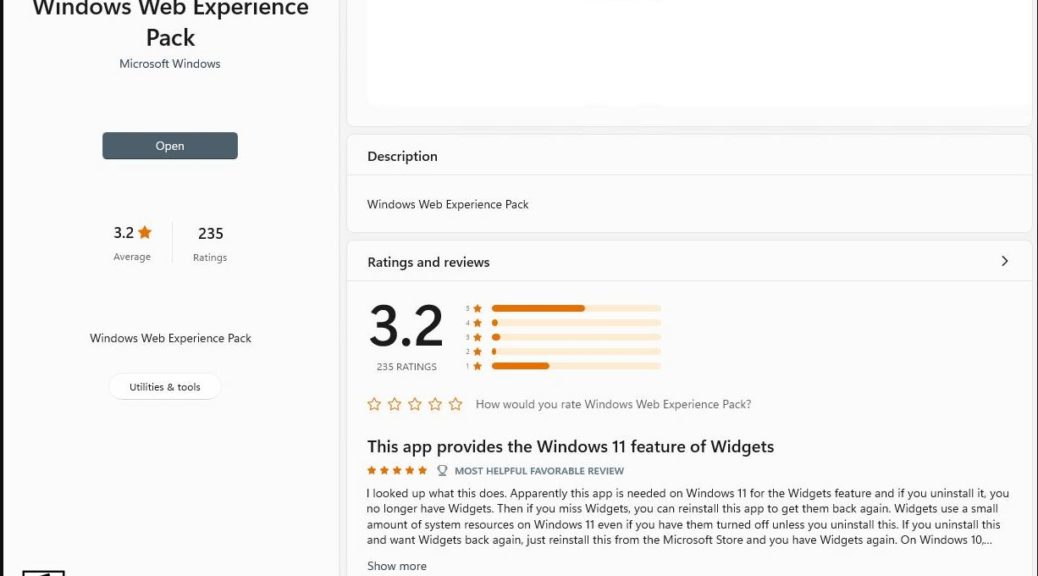
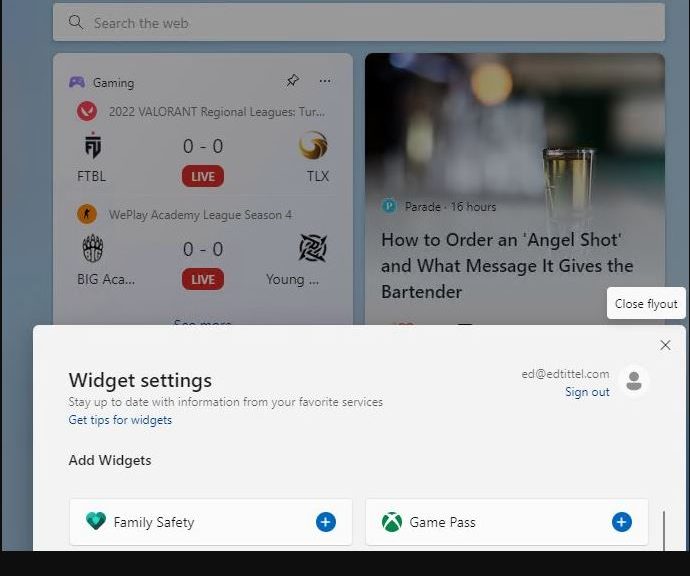
FYI, IDKT means “I didn’t know that.” I suspect the rest of the headline may likewise provide new info for other readers as well. This morning, I ambled over to the Store to check updates and a new Web experience pack update 421.20070.615.0 was applied. Just for grins, I visited the Store page and saw a user comment on this topic. It basically says “Windows Web Experience Pack Enables Widgets.” What of it?
What Windows Web Experience Pack Enables Widgets Means
The “Most helpful favorable review” under the WWEP feature also indicates that if one uninstalls it, Widgets quit working. And if one then restores the WWEP, Widgets return to work. Pretty conclusive, if you ask me.
So I went looking for MS “Official info.” And sure enough, here’s what it says on the MS Support page for WWEP update how-to:
Some Windows 11 features, like Widgets, are delivered through Microsoft Store updates. If you’re having problems with the Weather widget or aren’t able to find some features that were announced for Windows, you might need to update the Windows Web Experience Pack from the Microsoft Store.
Other than this support item and the Windows Store entry, though,. there’s surprisingly little info available about WWEPs.
Coming at Widget from the Development Side
OK, then. Knowing that MS is opening up widget development to third party developers, I instead went looking for related info. I found several interesting items:
- Windows.Developers: Latest Windows 11 features for developers (hmmm… nothing about widgets there)
- Windows.Support: Stay up to date with widgets (no mention of WWEP)
- Windows.App.Development: Create your first WinUI 3 (Windows App SDK) project (no mention of WWEP, or widget examples)
I’m not really seeing much useful description, examples, how-tos or other stuff to explain how third parties can build and deploy widgets. Maybe we’re not quite there yet? Hard to figure out what’s going on, if that’s not the case…