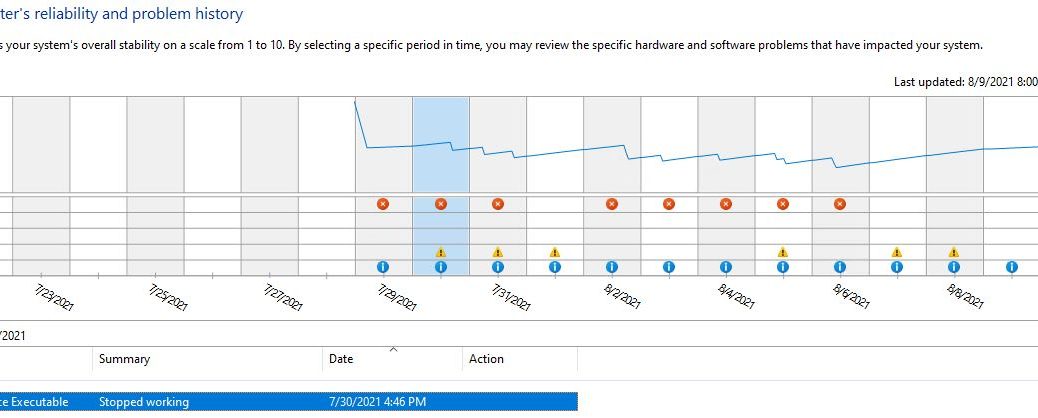
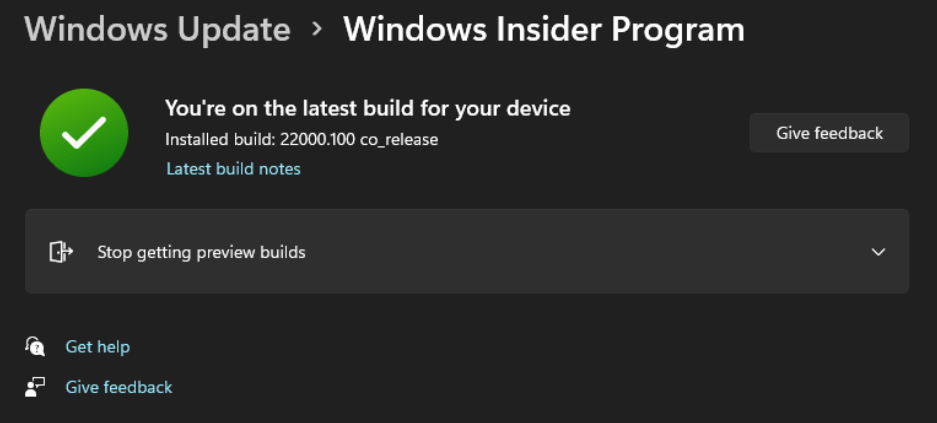
Back on August 9, I reported on some issues with the Lenovo firmware update tool, fwdetectcmd1911.ex, on my Windows 11 test PCs. I’ve given myself a quick self-help tutorial on the oustanding, highly-recommended UWP preview version of the Windows Debugger. It’s known as WinDbg Preview. It’s easily available from the Microsoft Store. And, unlike the old command line WinDbg, this version’s surprisingly easy to use. It’s what let me determine that Lenovo’s Win11 Firmware update causes momentary hiccups on my system. Why? Because the updater fails when it looks for Thunderbolt hardware and finds none.
When Win11 Firmware Update Causes Momentary Hiccups, No Worries!
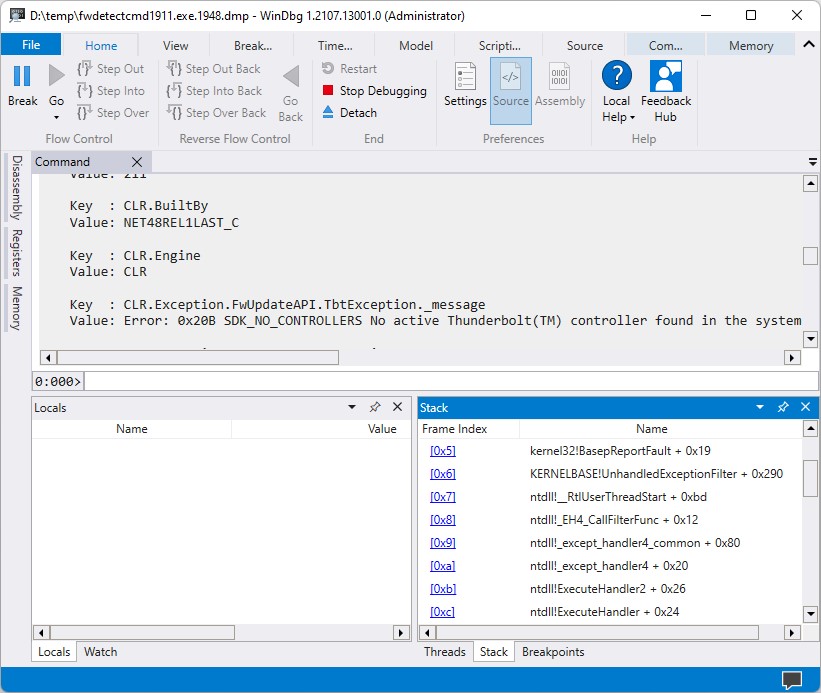
I’d been wondering if this was a serious problem. But a quick investigation shows that this condition throws an unhandled exception. In the Stack pane at lower left, a lengthy string labeled KERNELBASEUnhandledExceptionfilter appears right near the top of the error stack. That’s what tells me, along with the key value shown in the Command pane above, that missing Thunderbolt is my culprit. I guess I need to hook up a dock and try again so I can get past this recurring error.
Note the bottom error in the Command pane, and the second-from-top info in the Stack pane. Both tell a story of a crash when looking for absent Thunderbolt devices.
[Click image for full-sized view.]
I also plan to drop this info onto the Lenovo Forums so their engineers can get the word this is happening. I would imagine it will be pretty easy for them to skip over the Thunderbolt update if no Thunderbolt hardware is present, rather than throwing an unhandled exception. Time will, of course, tell if my imagining is mere fantasy or founded in fact.
All this said, I’m glad of a couple of things:
1. I’m glad that the recurring firmware update failures are an error in the updater and not indicative of a genuine system issue
2. I’m glad that I got a good excuse to try our the new WinDbg tool. It’s ever so much easier and fun to use than the old one.
And that’s the way things go here in Windows-World, with a smile and nod from yours truly today!