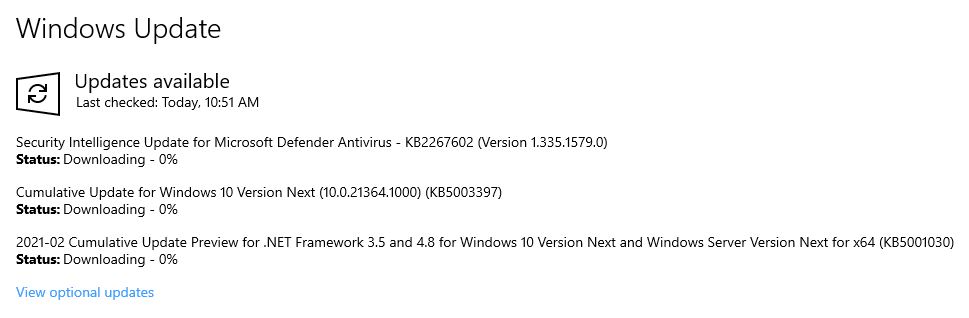
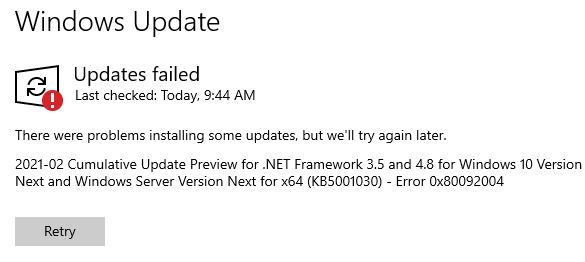
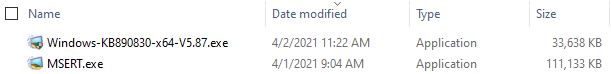
Here’s something I’ve not run into before. In trying to update my production PC to KB5001391 I found the download phase of the update stuck at 0% indefinitely. “No problem,” thought I, “I’ll download the .MSU file from the Microsoft Catalog.” Yeah, right!
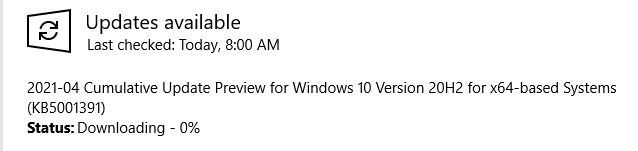
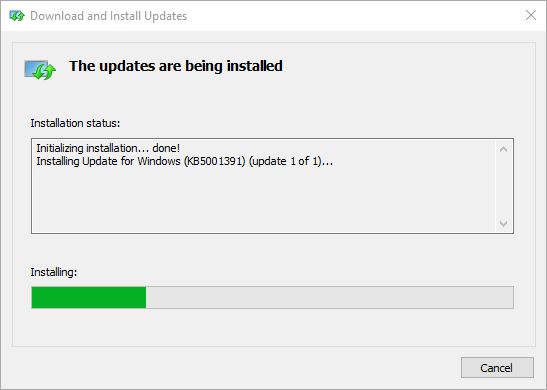
I guess the Catalog is smart enough to avoid duplicate, parallel downloads. It wouldn’t let me download the MSU file to that PC. So I jumped on one of my test machines, and downloaded the file there. Then I copied it over the network, and installed it by double-clicking its MSU file. This took a while longer than I was expecting (around 5 minutes or so) but it did work.
Why Update Download Stuck Forces Interesting Maneuvers
I can only speculate that WU informs the OS that it’s already downloading the requested KB item on that PC. Thus, clicking the download link from the catalog does nothing. That said, it worked as expected on a different PC, so I found a two-step workaround where a single step wouldn’t cut it. Please keep that in mind if you ever find yourself in this boat.
More Update Weirdness Follows
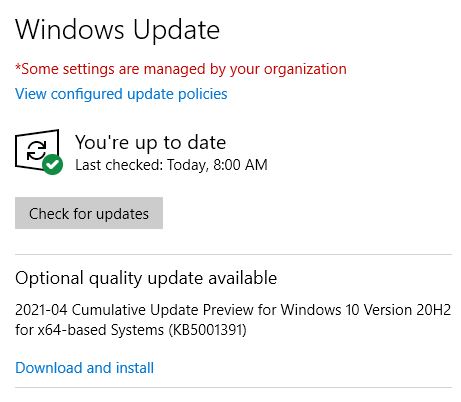
After the reboot to install KB5001391, I see it is installed in Update History. Nevertheless, Windows Update still shows me it’s available as an “Optional quality update…” (see screencap following).
Even though it’s already installed (and showing in Update History), I get another offer anyway. Sigh.
Of course, I am compelled to click the “Download and install” button to see what happens. When I do that, the Windows Update page comes back in about 30 seconds with nothing to download nor any status or error message to explain itself, either. I guess it figured out the update was already installed, and withdrew the offer. That’s a reasonably intelligent thing to do. Checking Reliability Monitor, I see no error reports about this there, either. So it looks like a clean save, so to speak. I’m glad!