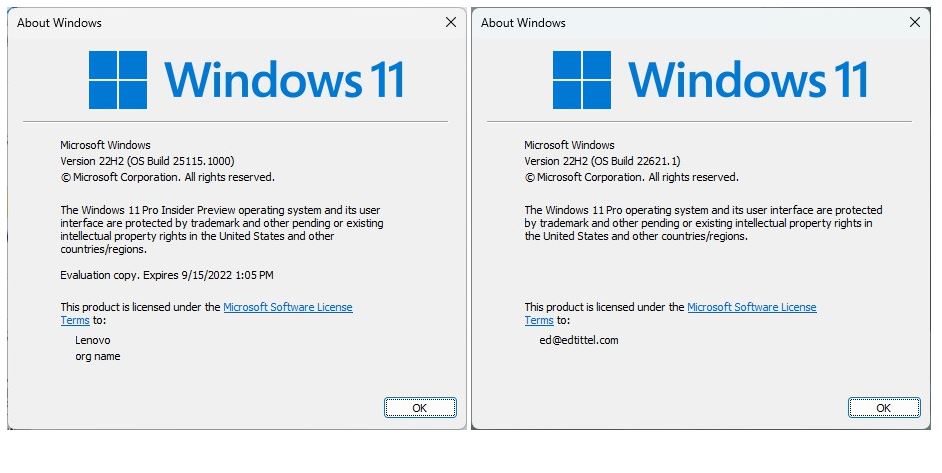
OK, what had been joined is now put asunder. Yesterday, Windows 11 Dev Channel went to Build 25115, and Beta Channel to Build 22621. This means that the two Insider Previews are now different. In fact, when Windows 11 Dev Beta channels diverge, it means they have different goals. According to WindowsLatest, 22621 represents a big push toward the first feature update for Windows 11. OTOH, 25115 shows that MS is still pushing forward into future releases looking into 2023 and the “next” feature update upcoming.
When Windows 11 Dev Beta Channels Diverge, Then What?
Among other things, this explains why MS broadcast an email warning to Dev Channel Insiders last week that “unstable and buggy preview builds will soon begin rolling out in the Dev Channel” (source: WindowsLatest, May 8). In other words, the Dev Channel is returning to its primary role as a “first exposure” to new features, functions, and whatnot making its way into limited circulation for testing and feedback. Frankly, I’m looking forward to this.
As for the Beta Channel, it’s gearing up for progressively more locked down snapshots of what will become the 22H2 release for Windows 11. Thus, it should become an increasingly accurate rendition of the next production Windows 11 release. Again: I look forward to this, too.
You can see the Winver output from these two different versions in the lead-in graphic for this story. The Dev Channel release (Build 25115.1000) is to the left.The Beta Channel release (Build 22621.1) is to the right.
Fun and Foibles A’Comin…
With a more freehwheeling and experimental take on Windows 11 coming to the Dev Channel, life is about to get more interesting. Who knows? There may be bugs or hiccups to detect and report, and trouble to shoot. That’s why I signed up for the Insider program, and why I’m looking forward to more new stuff ahead. Sure, there may be instability and bugs. But that’s a good thing in the interests of getting things out there, and then getting them right. Cheers!