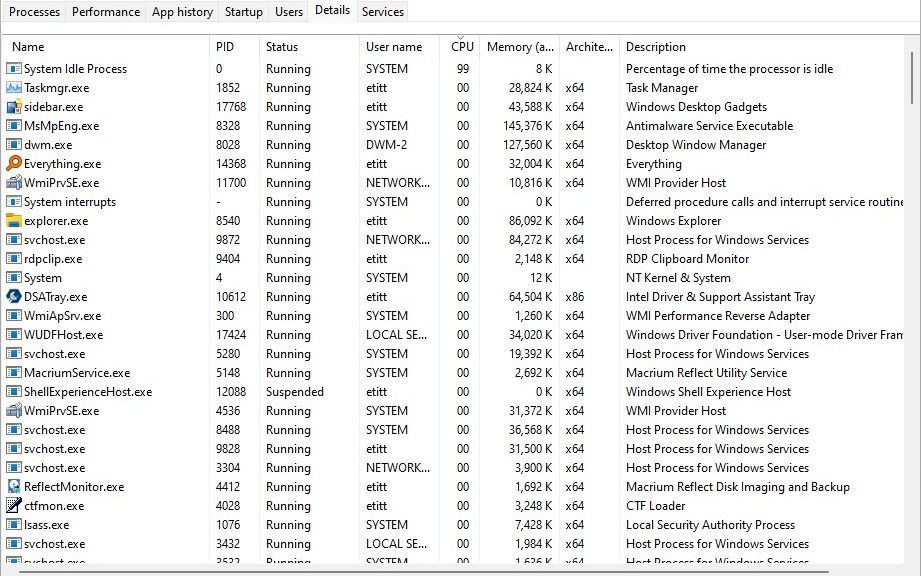
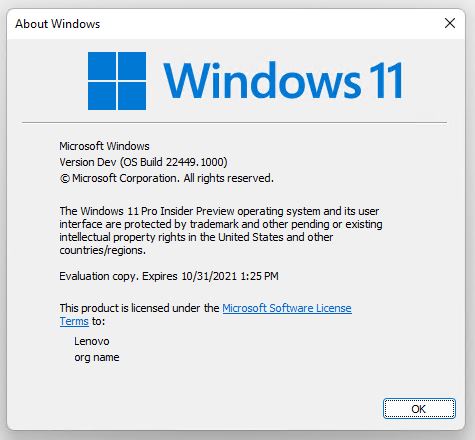
After upgrading my Lenovo X12 Hybrid Tablet to Windows 11 Build 22454 , I noticed CPU usage stayed elevated. For a long time, in fact: at least 5 minutes or longer. Checking Task Manager the culprit was obvious. Item software_reporter_tool.exe consumed half or more of available CPU cycles. Upon further investigation, I learned two things. (1) plenty of other people have experienced this. (2) it’s a part of Chrome’s Cleanup toolkit, designed to remove software that could cause potential issues with Chrome. Having just rebooted, Chrome wasn’t even running. But that apparently didn’t stop its background tasks from executing. And that, dear readers, is how I learned that sometimes the Chrome Software Reporter tool monopolizes CPU on Windows PCs.
Do This When Chrome Software Reporter Tool Monopolizes CPU
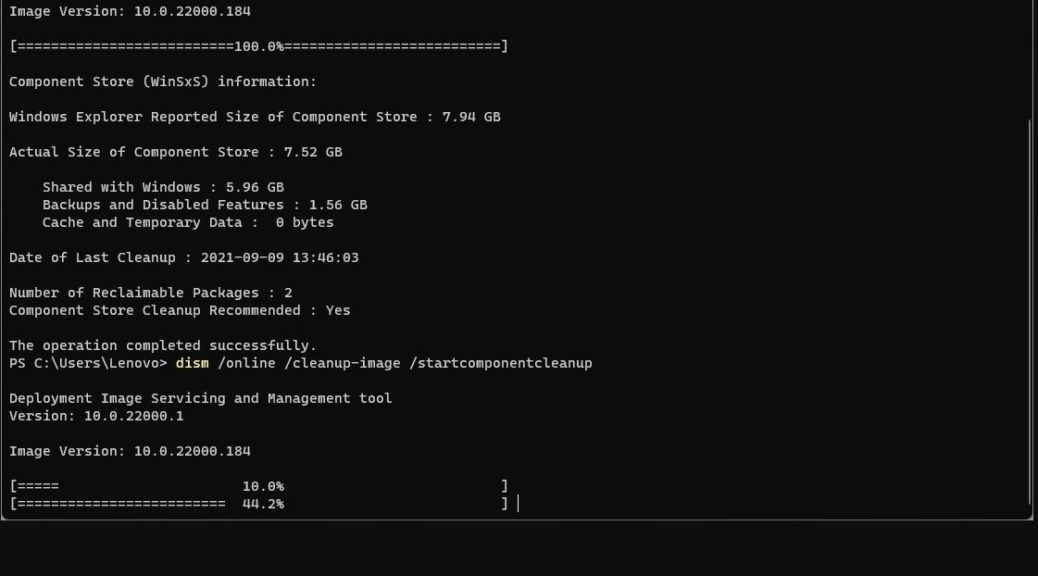
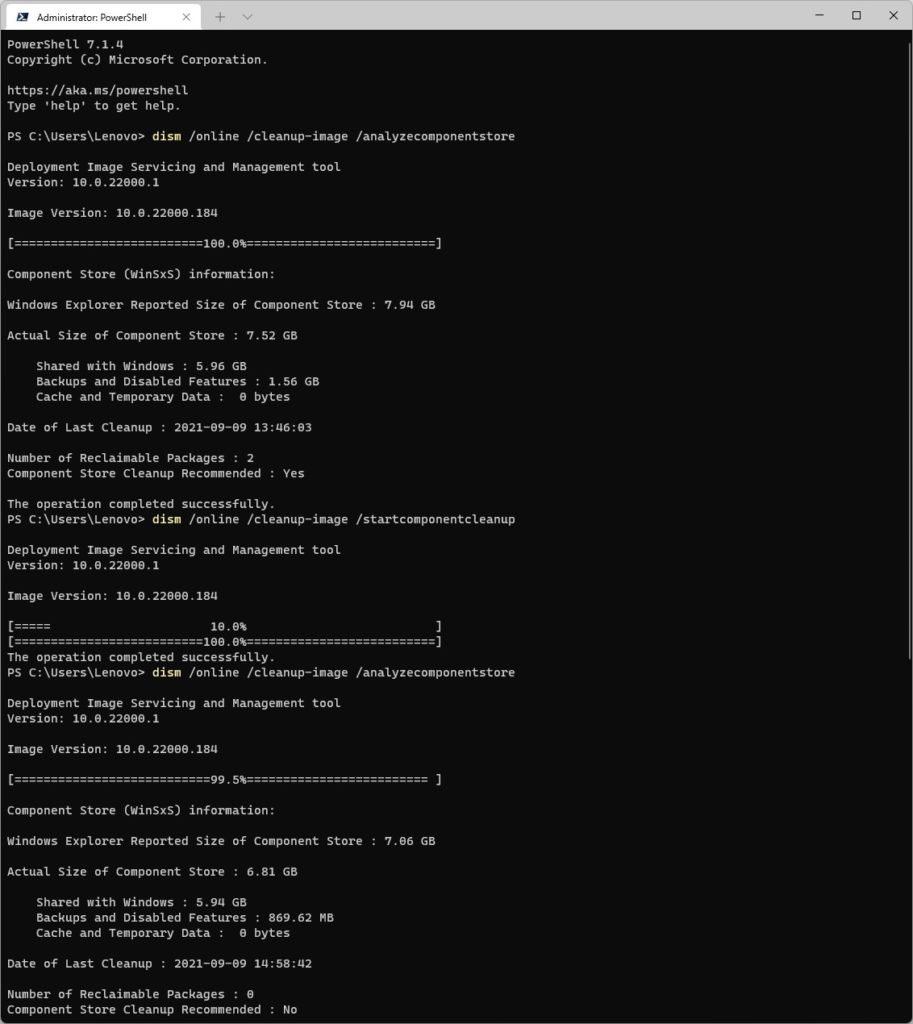
I found an article from Martin Brinkmann at Ghacks.net about this phenomenon dated January 2018. It provides a battery of potential fixes. These include a variety of blocking techniques based on file permissions, and Chrome policies (via registry hack). I actually found a 2020 Codersera article that offered a more direct approach.
It’s the one I implemented, and it’s working well so far:
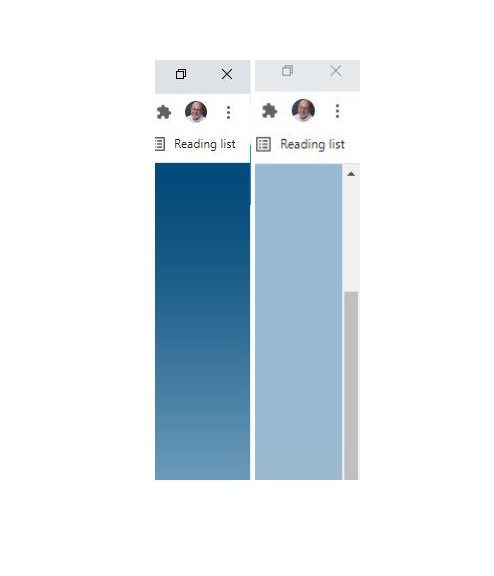
1. Open Chrome controls (vertical ellipsis symbol at upper left of browser window).
2. Click “Settings” resulting pop-up menu
3. Click down-arrow next to “Advanced” near bottom of that window.
4. Scroll down to “System” section and turn off item that reads “Continue running background apps when Google Chrome is closed” (move slider to left).
That should do it. At least, it seems to have worked for me: I haven’t seen any recurrences since I made this configuration change.
When Odd Processes Stand Out, Research Helps
This technique is a familiar one to those keep an eye on Windows performance. It’s often a good way to start digging into slowdowns like the one I ran into last week. I generally try to rely on well-known and -respected resources when it comes to fixes (if not the maker or vendor’s own tech support info). But usually, when there’s a will to fix such things, a way to fix them can be found.
If worst comes to worst (and I have a recent backup) I might even right-click the offending process and select “End process tree” to see what happens. Please note: don’t do this with Windows OS components, or you’re likely to experience a BSOD. ‘Nuff said.