Before we dig in, let me define the terms in the title so nobody gets left behind. OCuLink — short for “Optical-Copper Link” — uses the SFF-8611 and SFF-8612 cable specs, originally bred in the enterprise SAS and NVMe world, and now showing up on consumer PCIe expansion cards, eGPU docks, and mini-PC expansion modules. The reason OCuLink offers a viable TB4/5 aleternative is: it carries native PCIe lanes over a compact four-lane connector. Zero protocol translation is involved.
TB4 is Thunderbolt 4 — Intel’s certified 40 Gbps interconnect standard. It runs the Goshen Ridge controller and dominates today’s laptops and docks. TB5 is Thunderbolt 5, Intel’s 80 Gbps follow-up, running the Barlow Ridge controller. It started appearing on premium Copilot+ laptops and high-end docks in late 2024.
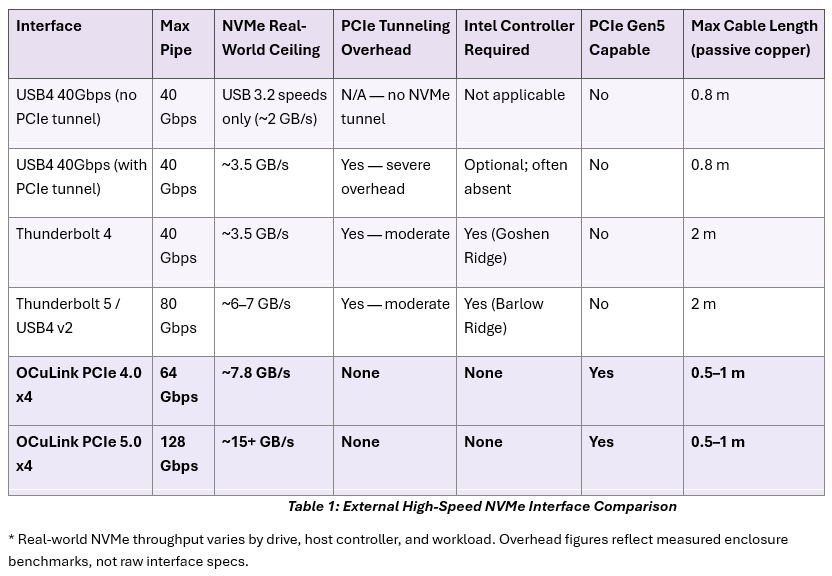
Intel has owned the high-speed external storage conversation for nearly a decade. I must ask: “Is there a credible alternative path for builders and prosumers who’d rather not pay the Thunderbolt toll?” Table 1 above says yes, emphatically. The rest of this post explains why the math works out that way.
Why OCuLink Offers a Viable TB4/5 Alternative
Start with the Intel moat, because it’s real and it matters. Thunderbolt certification ties nominally to the USB4 spec. In practice, Intel controls the gate through its mandatory certified controller requirement — Goshen Ridge for TB4, Barlow Ridge for TB5. Each controller adds $15–$25 to a device’s BOM. That cost tags along through the supply chain straight to your invoice. The certification program itself isn’t free either, which is why you see so many USB4 ports on budget laptops and mini-PCs that carry the USB4 badge but quietly skip PCIe tunneling entirely — because PCIe passthrough is optional in the USB4 specification. A port can wear the USB4 label, deliver USB 3.2 storage speeds, and be perfectly compliant. Go figure! Intel doubled the bandwidth ceiling with Thunderbolt 5. But the same certification architecture stayed intact. That structural dependency hasn’t gone anywhere.
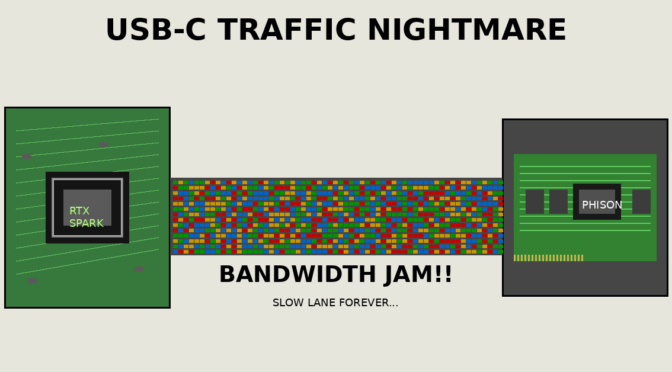
The Tunneling Tax
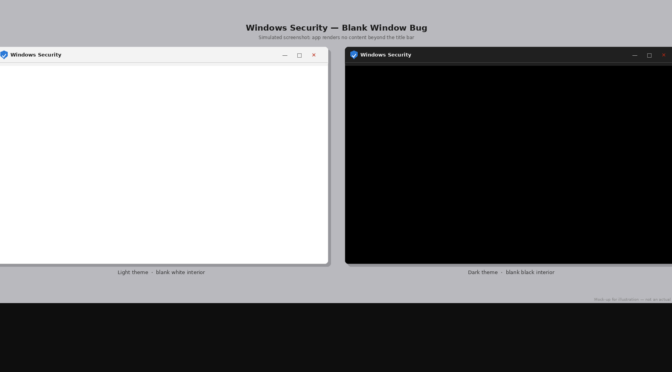
Then there’s what tunneling costs you, and this part tends to get glossed over in spec-sheet marketing. Both TB4 and TB5 move PCIe data over a tunneled protocol stack built primarily for display connectivity. The protocol treats NVMe storage as a secondary concern. That overhead carries a measurable real-world cost. TB5’s 80 Gbps headline pipe delivers only around 6–7 GB/s to an NVMe enclosure in independent benchmarks
Alas, this lands below the sequential read ceiling for a single Samsung 990 Pro or WD Black SN850X. The bandwidth also gets split in ways the spec sheet doesn’t advertise. Run a TB5 dock with a 4K display and a storage enclosure at the same time. The NVMe gets whatever lanes aren’t already committed to display output. No firmware update can fix that. It’s simply how the tunneling protocol divides resources between display and storage traffic.
OCuLink sidesteps all of it, and the reason is almost embarrassingly simple: it carries native PCIe — no tunneling, no overhead, no protocol translation between the cable and the drive controller. The SSD on the far end of an SFF-8611 cable sees the host’s PCIe bus directly. It behaves exactly as if it were seated in a motherboard M.2 slot.
You need no Intel controller, no certification fee in the BOM, and no spec-version negotiation between host and peripheral. Any PCIe host with an SFF-8611 port talks to any OCuLink enclosure. The connector standard is generation-agnostic. OCuLink scales to PCIe Gen5 today, with a theoretical ceiling over 15 GB/s. Thunderbolt 5 can’t get close within its tunneling architecture. Intel spent a decade building a toll road. OCuLink is the county road that goes to the same place, faster, for free.
What Are OCuLink’s Trade-Offs?
I’d be doing you a disservice if I left it there. That’s because OCuLink’s edge comes with genuine limitations you need to price into a buy-in. Cable length is the hard ceiling for which there’s no current engineering workaround. Passive copper OCuLink tops out at 0.5 to 1 meter depending on implementation. TB5 copper passive reaches 2 meters. TB5 optical reaches 40 meters or more. For a storage enclosure sitting six inches from your PC, cable length is a non-issue. For anything across a room or mounted in a rack, it’s disqualifying. Know your use case before you order anything.
Hot-plug behavior is the next honest caveat. PCIe never supported hot-swapping natively. OCuLink inherits that reality. Some enclosure implementations handle safe removal gracefully through driver-level coordination. Others expect a full shutdown first. At minimum, eject the device properly from Windows before pulling the connector. TB4 and TB5 hot-plug is standardized, reliable, and boring in the best possible way. You unplug, Windows notices, the drive disappears from Explorer. No drama.
Ecosystem and Power: The Remaining Gaps
The OCuLink consumer ecosystem is thin compared to Thunder-bolt’s. The OCuLink ecosystem embraces dozens of enclosures from small-batch vendors. Thunderbolt counts hundreds of certified peripherals from Belkin, CalDigit, OWC, and others. Support responsiveness, documentation quality, and return policies reflect that gap. Also, OCuLink carries no power delivery over the connector itself — any drive or enclosure needs its own power source. TB4 and TB5 deliver up to 100W over the same cable that carries data. None of those are dealbreakers for a desktop prosumer. They could be for a road warrior expecting plug-and-play.
For desktop and prosumer builders, or anybody running a PCIe expansion card that exposes an SFF-8611 OCuLink port, you get a legit, lower-cost, higher-throughput alternative to Intel’s certified Thunderbolt ecosystem. The bandwidth math in Table 1 speaks for itself. OCuLink over PCIe 4.0 x4 already beats TB5’s real-world NVMe ceiling. PCIe Gen5 doubles that figure again with no new Intel controller, no certification program, and no tunneling tax required. Those are the deets. Intel built the tollbooth. OCuLink is the on-ramp they forgot to close.
It’s worth considering, and maybe buying into. I’m doing just that myself. You may want to do likewise, if you like the numbers as much as I do.